Quick Start
If you don't want to delve into the details of our protection mechanisms, simply follow these brief steps when using DotFix NiceProtect for a basic protection:
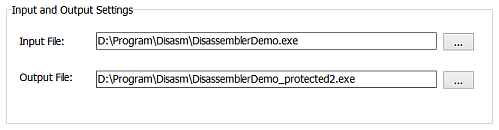
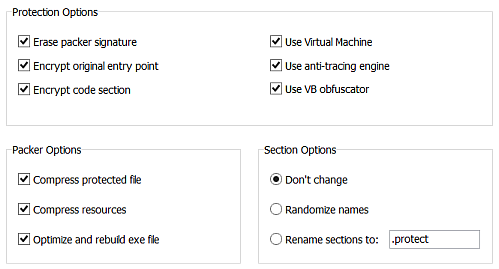
We want to reiterate that basic protection features of the DotFix NiceProtect does not require any changes to your program's code. Simply open your program in the software protector, follow our step-by-step instructions, and you're good to go! When it comes to protection options, we recommend selecting packing to reduce your program's size. Additionally, you can choose to add anti-tracing and obfuscation to deceive debuggers and decompilers - this options highly recommended for added security.
If you would like your program to display a startup message next time, please leave the Use startup message checkbox selected. Alternatively, you may clear the checkbox if you prefer not to have a message displayed upon starting the program. The message can be customized with the following text:
You are currently using the DEMO version of this program,
which has several limitations. To remove these restrictions
and enjoy the full functionality of the software, please visit
our website at www.oursite.com to make a purchase.
You may also configure your own custom messages in the Custom Messages section.
Startup message:
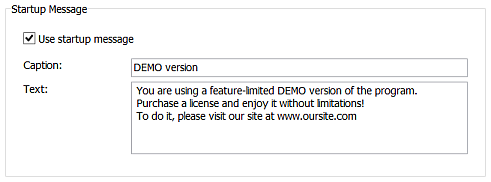
The effectiveness of this message is quite significant. Each time a customer starts your program, they will become increasingly frustrated with the persistent reminder. However, if they need the product, they may consider purchasing it and potentially becoming your client in the near future.
To implement these simple steps, you will need to go to the Custom Messages section and select the desired message for display upon startup. Once completed, proceed to the Protection tab and click on the Start button. The software protection process will begin, providing detailed information about the protection progress:
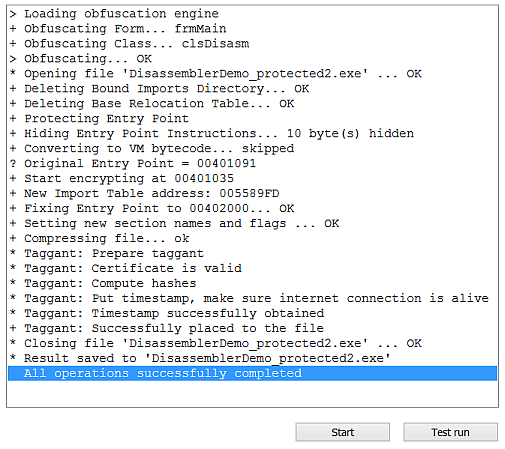
It is essential to note that this basic protection option may not be sufficient for comprehensive software security. We highly recommend exploring additional features such as function protection using MAP files and code virtualization with markers for more robust protection.
Virtualization markers can help protect critical codes within your software, while selecting all critical functions at the Code Protection tab for virtualization by DotFix NiceProtect engine is also strongly recommended.