Protection options
This set of options enables you to fully customize the security level for your program. From simple encryption of a few bytes at the entry point to the Virtual Machine technology with complete encryption. Learn more about each type of option below.
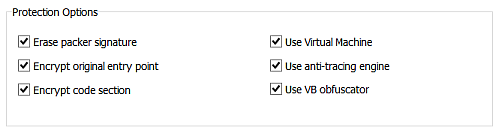
- Erase packer signature
This feature is only useful if you use any third-party EXE packer (which we do not recommend unless you want to ensure no errors in protection) before running your program through this security tool. By erasing the signatures of popular packers, it prevents crackers from automatically unpacking your program.
- Encrypt original entry point
This option encrypts a few bytes at the entry point of your program, providing an additional layer of security.
- Encrypt code section
By protecting the code section against analysis by crackers, this feature ensures that even if someone uses a disassembler to analyze your program, they will not be able to understand it due to encryption.
- Use Virtual Machine
The main idea behind using a virtual machine is to translate part of the code located after the entry point (from 10 to 500 bytes depending on the set of commands) into metamorphic instructions and then partially compile them into code that only the VM interpreter can understand. This interpreter is built into your program and interprets these blocks of commands, making it more difficult for crackers to explore your software.
- Use anti-tracing engine
This feature prevents crackers from tracing your program by incorporating numerous tracing checks (tracing means debugging the program code step by step) within your program. This makes exploring your program much more challenging.
- Use VB/RTTI obfuscator
By activating this checkbox, you can utilize a powerful obfuscator for Delphi, C++ Builder, Free Pascal and Visual Basic 5.0/6.0 applications. This obfuscator changes all names of forms, objects, unit declarations, and event names to make it more difficult for crackers to understand your code.